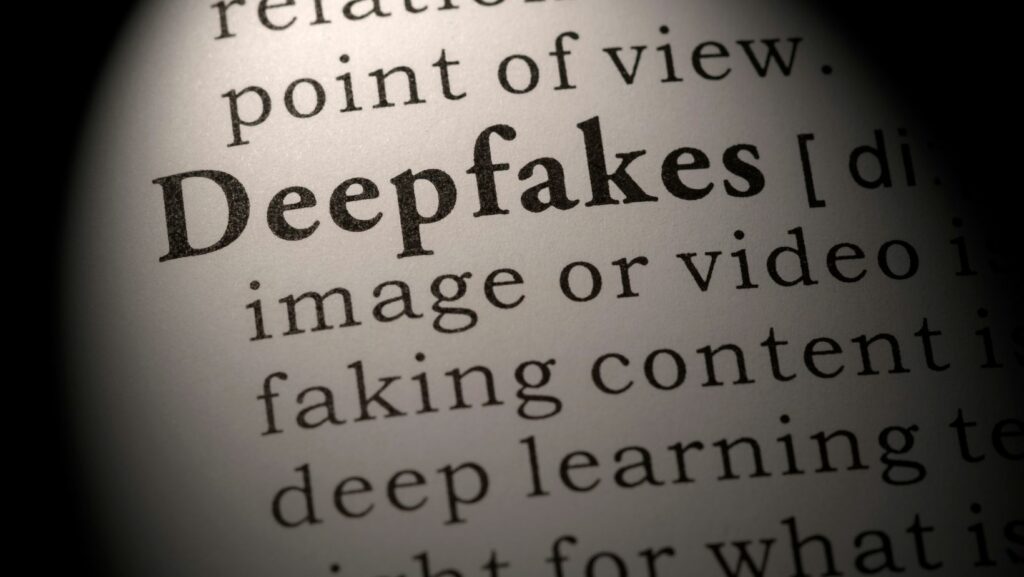
 Think for a second that you’re scrolling through your feed, and you suddenly see an obscene video of your favorite celebrity pop up. The video is too unbelievable to be true, and yet it looks too real to be false. Or maybe you saw a video clip of a politician committing a crime that went viral and shot their reputation down. Well, Black Mirror’s predictions of such a technology are here in the form of deepfakes.
Think for a second that you’re scrolling through your feed, and you suddenly see an obscene video of your favorite celebrity pop up. The video is too unbelievable to be true, and yet it looks too real to be false. Or maybe you saw a video clip of a politician committing a crime that went viral and shot their reputation down. Well, Black Mirror’s predictions of such a technology are here in the form of deepfakes.
The bad news? Deepfakes are on the rise. Shocking findings from the Global Incident Response Threat Report show that 66% of cybersecurity professionals have come across these deepfakes in attacks, often delivered via email. Deepfake cyberattacks are more dangerous than we think, but you know why? Because organizations are not prepared to protect, predict, and mitigate these attacks from happening, like a risky game of Russian Roulette where nobody knows whose next.
The good news? You can learn to identify and avoid them. Let’s dive into how to protect yourself from this evolving threat.
Understanding Deepfakes: A Technical Breakdown
Do you know how deep fake videos are made? They use a technology called GANs or Generative Adversarial Networks to create these artificial videos. This can be applied to audio, video, and images that seem quite credible. What you eventually have is a situation where you view all news, especially video content, with a sense of distrust. In essence, they undermine the credibility of all information.
The amazing thing is that people tend to retain false information even when they are told that the information is fake. So deepfake videos tend to create false memories. And in this age of information overload, we are often confused about what is genuine news and what is fake. So now deepfake videos are playing games with our minds.
How Are Deepfakes Created?
Basically, deepfakes are created using Generative Adversarial Networks. This consists of two elements: the Generator Algorithm and the Discriminator Algorithm. The generator program creates a fake video, image, or content using previously known information about a person and content or issues that they are connected with. It copies mannerisms and styles as closely as it can. The discriminator program is even scarier. It uses machine learning to evaluate the iterative video, updating and modifying it until it results in content that it believes is good enough to be finally generated.
Deepfakes pose dangers to cybersecurity.
Spreading False Information
When deepfakes are used to spread false information by creating fake video or audio content, they can malign people’s reputations and affect opinions about them.
Invasion Of Privacy
Deepfake technology can be used to manipulate people’s videos or images, leaving them open to blackmail or harassment.
Implicating People In Fraudulent Activities
Unscrupulous individuals could create videos implicating innocent people in fraudulent activities, causing confusion for law enforcement officials.
Affecting Political Events
There is a danger that creating false speeches or events could sway voter opinion and affect the political results and the future of nations.
So, as deepfake technology improves, it poses more and more threats and challenges for cybersecurity.
Building a Defense System: Practical Steps to Stay Safe
Given the increasing threats to cybersecurity, here are some practical steps to stay safe from such malicious content.
Use Technology To Detect Deep Fakes.
The first thing you can do is to look for inconsistencies in video or audio content. These can include such things as jerky face movements, mismatch of lip-syncing, irregular lighting or unfamiliar environments, excessive blinking, or other body movements that seem unnatural. Although technology exists that can analyze video content to recognize deepfakes, they may soon be undetectable as deepfakes get more and more accurate.
Train Staff To Recognize Deep Fakes
It is important that staff learn to identify deepfakes whenever possible. The creation of policies with reporting criteria will alert officials to the existence of such material. People must know who to go to if they are unsure of the authenticity of video and audio content. One should always double-check before releasing funds, giving access to confidential information, or creating new contracts for vendors.
Make Use Of Digital Signatures.
One of the ways to identify authentic content is to use digital signatures. When you create video or audio material that has a digital signature, it creates a hash for verification that is unique and can’t be duplicated. Digital signature certificates are time-stamped and reveal the maker and source of the document. Artlogo has its own online signature generator program that can generate unique digital signatures. This can easily be appended to any written document, presentation, audio, or video. What’s more, it can reflect your personality while being an effective cybersecurity tool.
Industry Policy Measures
There have been concerted efforts by governments and public and private enterprises, as well as security watchdogs, to institute policies that control AI content and make them conform to ethical and security standards.
However, the rules and laws have not been applied stringently. There has also been a move to regulate AI and LLM providers to mark deepfake content so that it can be identified and controlled.
Keep A Record Of All Appearances.
It is important to keep a record of all appearances of speeches, audio, and video of key personnel. These can be accessed when needed so that real footage can be compared with potential deepfakes to reveal discrepancies. It is also necessary to constantly monitor all media and social channels to identify false information and mitigate its negative effects. If the public knows how to identify and shun deepfakes, it would be great because the problem would be nipped in the bud.
Conclusion
We have looked at how deepfakes are created and the way they can be used to malign reputations and sway public opinion. This is why they pose a great threat to cybersecurity. Educating people and staff on how to spot deepfakes and instituting policies to control its spread both at the organizational and governmental level will go a long way in protecting us from the malicious effects of this technology.